Have you noticed that the most recent reports of email scams seem to be more personal/targeted attacks? Do you feel that scammers know you? That’s because they do know you.Office 365 gives malicious agents a way to spy on you. If you don’t believe us, just google it yourself and you will see reports of Office365 vulnerabilities, hacks and exposures. Just type “Office365 security vulnerabilities” and skip paid ads section.
Do you use Office365? If the answer is yes, Digital Edge would like to raise awareness to you regarding a new upcoming way of being hacked and then be under surveillance through your email. Take a look at the sample rule created below:
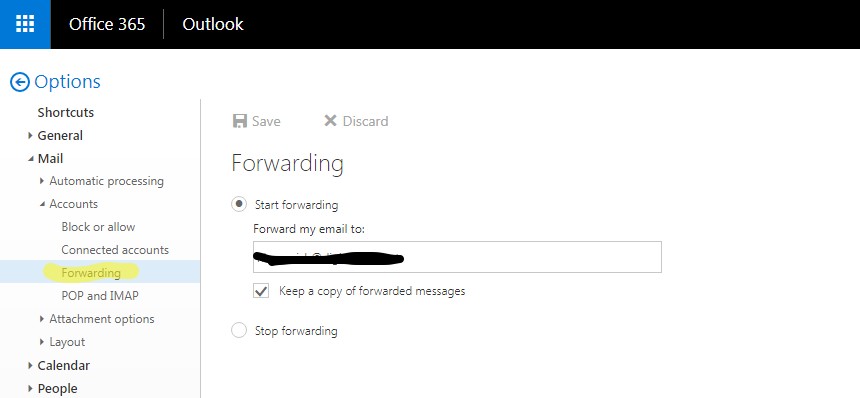
This screenshot shows how unnoticed rules were installed inside of the O365 email box. This example shows how the hacker installed a forwarding rule to copy all of the users emails in the inbox to an outside email address.
Another example is below:
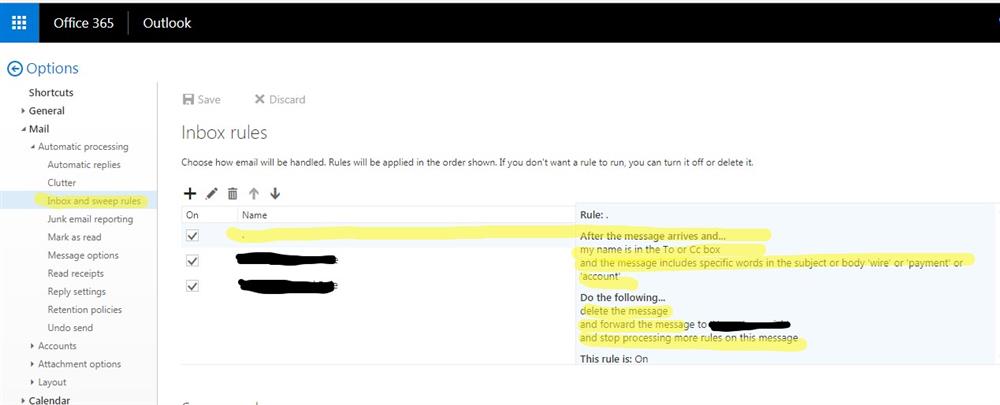
In this example, specific emails that are recognized as financial, client related communication or passwords are silently redirected to an attacker.
If you see something similar in your email box and you don't recognize what it is – it might be a sign that your email conversations are under a hacker’s surveillance.
An email attack in Office365 that involves setting up an invisible “forwarding path” rule- the hacker makes sure all your emails are directed to them as well. This can lead to:
- The attacker being able to see all your personal/business emails and conversations where he/she can get vital information on you or your business, and use it later in scams to trick you to send money to a wrong bank account or company that would be similar to your vendor or a partner.
- The attacker being able to pull money out of you, just stealing your personal information, passwords, accounts etc.,
- And when the hacker sets this up, the user is completely unaware that this “forwarding path” rule has been established.
- After gaining enough information, they will try to pose as someone they are not and trick you into giving them vital information.
The majority of people use Office365 without the thought of being hacked ever crossing their minds. Because of this, it is very easy to become victim to these attackers. And there have been very serious, very extreme cases of people and companies losing thousands of dollars to these attackers.
One of our clients noticed a possible exposure to O365 weakness and engaged us. This was their post statement:
“Digital Edge has provided exemplary technical solutions and monitoring that have provided us with an effective means of tracking attacks which utilize the recent Office 365 EWS vulnerability.” - JG, SVP of Information Technology
Just this week, another one of our clients experienced this same issue. [We will not be mentioning names to keep client confidentiality as requested] The client received an email from a past employee asking for an invoice. Without checking, he clicked on the link. He later confirmed with the past employee that the email was spam, but whoever send the email has already gotten all the information they needed. Later our client received a call to confirm a wire transaction of around $38,000 to a bank account in Texas. When our client tried to find the email again, it was missing. Our client came to us asking for help, where we found out that the emails relating to this scam were marked to be deleted upon arrival.
Although this issue is now resolved, our client has had dozens of people coming to him, claiming they received the same email from him. Digital Edge has seen similar and even worse case scenario’s. We are trying to make sure everyone is well aware, informed and protected against this rising issue.
These types of attacks happen every day and awareness is the first step in being protected. Other solutions can be costly; but we at Digital Edge value our client’s safety and recognize the importance of it. Digital Edge understands that keeping your emails private and only for the view of the intended is very important as emails can be very topic sensitive. We are giving out the scripts to secure your Office365 free to download after you register. If you need technical assistance in securing your Office365, Digital Edge is here to help, just contact us directly through our website! If you want more technology information, Digital Edge has methodologies and tools that we give to the community for free once you register!
