You have your corporate email defenses lined up. While you may be using an out of the box product such as Microsoft O365 or something more sophisticated like ProofPoint – here is what you need to know.
Although you might be as safe and secure as possible you should still be aware of the vulnerablities that exist and can affect you.
Unless users are restricted from using mobile email apps, there is nothing that can protect you. This risk extends even to disclosure of your corporate authentication.
The Thought Process (it will become more complex):
If I am a hacker, here is the easiest way to harvest login information – I create my own email application and just collect clear UID/PWDs of the users who download the app. Users configure their access to their corporate emails (they login to their email accounts) and done – I have the credentials of someone's corporate network. Today most email services are integrated with corporate security, however, someone's information can be totally disclosed through an email application.
Putting it into Real Life Perspective:
Today, there are many mobile email apps that are available on Google or in the Apple App store for download. They use proprietary mechanisms to synchronize your corporate email box with the email app that's on your mobile device.
During our recent reviews of client access to corporate messaging infrastructure, we have discovered that some email apps are CACHING THE FULL CONTENT of your email boxes on to THEIR CLOUD SERVERS. In the case of O365 or Exchange some mobile email apps sync EVERYTHING WITHOUT YOUR knowledge and APPROVAL including calendars, notes, clients, public folders, etc.
In simpler terms: ALL of the content from an employee's email box will be downloaded on to a third party server.
Here is a visual example of what is going on.
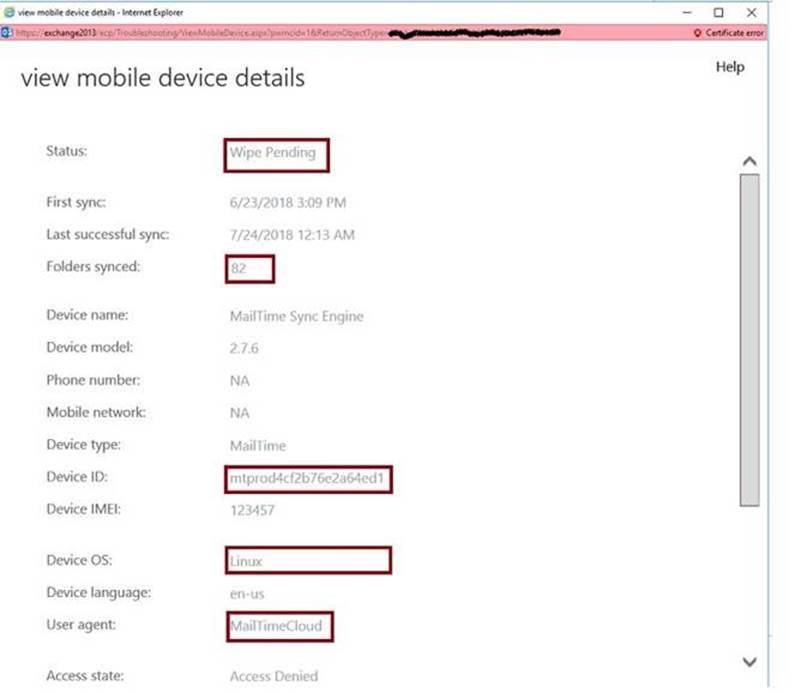
As you can see, this user installed an email app to his mobile device and after providing his credentials, 82 folders were cached from Exchange to a cloud server. IP logs were showing that they're located in a third-party server.
It's alarming that without our knowledge and consent, email apps are able to make unauthorized copies of everything in someone's email boxes and hold them in third-party servers. We also have no way of knowing what the third-party servers are planning on doing with our information as well as what types of security measures they have in place to prevent a breach.
In addition to this, Digital Edge's security team has seen servers or third-party email providers hacked. So far, our team has seen examples where hackers were sending viruses through those third-party servers on behalf of employees, but there is no knowing what else the hackers will do. We haven’t seen any evidence yet that hackers could get to user’s data cached on such servers, however as we mentioned, we don't know what kind of defense mechanisms these third-party servers have set up.
These controls CANNOT be covered by information security systems such as NIST or ISO.
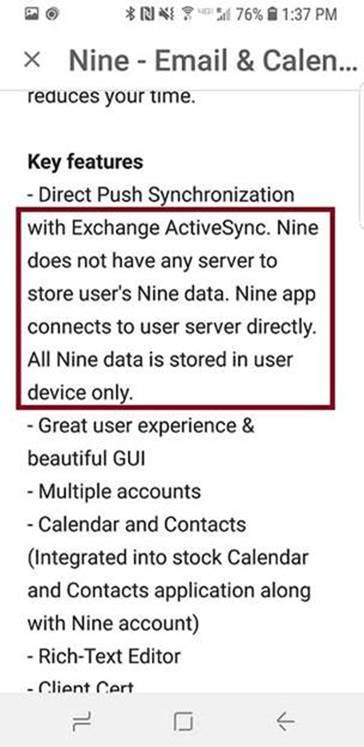
Moreover, email app providers do not disclose the fact that they use third-party servers or cache content onto them. However, some email apps will disclose clearly that they WILL NOT cache the content on their servers.
Here is an example:
At this point, we don’t have any automated solution to this problem other than creating corporate policies prohibiting employees from installing email apps of their own choosing.
Only careful review of logs can reveal such security problems.
Digital Edge constantly and consistently provides review of clients security. To ensure the security of our clients’ data, we keep up to date with the most recent breach reports and we research and analyze new ways in with which hackers might attack before they attack. Although there is no protection from this way of hacking, being aware of this can prevent you from downloading potentially dangerous apps.
Digital Edge operates a complex, geographically diversified Elasticsearch/Logstash/Kibana cluster that is used to collect and securely store our own and our clients’ logs. Every client’s logging, storing, and indexing activities are fully managed by Digital Edge. Digital Edge also offers cyber security to our clients, which includes penetration testing, alert analysis, incident responding and 24/7/365 monitoring. For more information about our IT security services, you can visit our website or contact us to speak to an IT consultant today!

